Identify Unused Service Accounts in GCP
Many organizations struggle with “credential sprawl”; an unmonitored, untracked growth of Identity and Access Management (IAM) credentials throughout their cloud environment. This is especially true in Google Cloud Platform (GCP), where in addition to users and groups, you also have service accounts. There are many tools available to assist with identifying where credentials are located, but not many that provide data on when a credential was last used. In GCP, there is a service called Recommender, which has a feature, Service Account Insights, that helps identify unused service accounts in a GCP organization that have not been used in the past 90 days.
This article will walk you through how to enable Recommender, identify unused service accounts in your project, as well as identify unused service accounts across your entire GCP organization so you can keep credential sprawl in check!
Enabling the Recommender
If you are unfamiliar with the Recommender service we recommend spending about five minutes reading up on the offering.
In order to use services in GCP (outside of the defaults) they first need to be enabled. Enabling the Recommender service is fairly straightforward via the gcloud CLI. First, you need to set the project you’d like to enable the Recommender on:
gcloud config set project PROJECT_ID
Next, enable the service:
gcloud services enable recommender.googleapis.com
You may be asking yourself, “do I have to do this for every project?” The answer is yes, but, you can make this easier on yourself with a for-loop:
| #! /bin/bash | |
| for id in `gcloud projects list --format="value(projectId.scope())"` | |
| do | |
| echo "Enabling Recommender on project ID: $id" | |
| gcloud services enable recommender.googleapis.com --project=$id | |
| done |
Keep in mind that you will need permissions to list every available project as well as permissions on those projects to enable services. You can read more about the permissions related to enabling services here.
Viewing the Service Account Insight
The Recommender service currently offers one subtype for the Service Account Insight: SERVICE_ACCOUNT_USAGE. SERVICE_ACCOUNT_USAGE will tell you which service accounts have not been authenticated (used) in the past 90 days. To view the SERVICE_ACCOUNT_USAGE subtype, for the Service Account Insight, you need specific IAM permissions. For the Service Account Insight, you need:
recommender.iamServiceAccountInsights.getrecommender.iamServiceAccountInsights.listrecommender.iamServiceAccountInsights.update
Once you have the correct permissions you must use the gcloud CLI to view the insights, they are not currently available in the console:
gcloud recommender insights list \
--insight-type=google.iam.serviceAccount.Insight \
--location=global \
--filter=insightSubtype=SERVICE_ACCOUNT_USAGE
If there are any SERVICE_ACCOUNT_USAGE subtypes for the Service Account Insights in your project they will look similar to this:
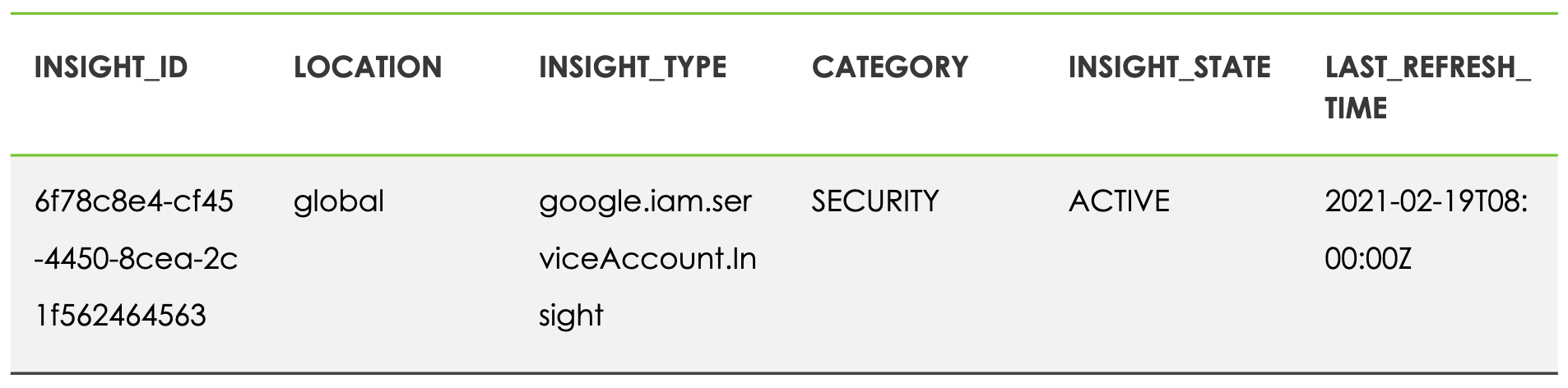
Service Account Insights
By default that doesn’t provide you with a lot of actionable information, but with one flag you will receive much more:
gcloud recommender insights list \
--insight-type=google.iam.serviceAccount.Insight \
--location=global \
--filter=insightSubtype=SERVICE_ACCOUNT_USAGE \
--format=json
Now returns:
[
{
"category": "SECURITY",
"content": {
"email": "example-email@appspot.gserviceaccount.com",
"serviceAccountId": "10951235633"
},
"description": "Service account example-
email@appspot.gserviceaccount.com was inactive.",
"etag": "\"145eff595a10517c\"",
"insightSubtype": "SERVICE_ACCOUNT_USAGE",
"lastRefreshTime": "2021-02-19T08:00:00Z",
"name":
"projects/1234567890/locations/global/insightTypes/google.iam.ser
viceAccount.Insight/insights/6f78c8e4-cf45-4450-8cea-2c1fa7c729b8",
"observationPeriod": "29725200s",
"stateInfo": {
"state": "ACTIVE"
},
"targetResources": [
"//cloudresourcemanager.googleapis.com/projects/1234567890"
]
},
We can now see that we have a service account in our project that has not been used in the past 90 days. The insight also provides us with the project number where the service account is located so that you can track down the owner and make a risk-based decision on if the service account can be removed.
Viewing All Unused Service Accounts
Now that you know how to locate and identify unused service accounts in a single project, we will explore how to view ALL unused service accounts in your GCP organization. At ScaleSec, we regularly assist companies with credential sprawl and have open-sourced one of the scripts we use on our GitHub page.
Once you have enabled the Recommender service across your entire GCP organization you are now prepared to find each and every unused service account using one script. First, you need to clone the repository:
git clone [git@github.com]:ScaleSec/gcp_sa_lister.gitNext, create your python virtual environment:
python3 -m venv ./venv/
source ./venv/bin/activate
Finally, install your libraries:
pip3 install -r requirements.txt
You are now ready to execute:
python3 saUnused.py
For every project in your GCP organization, the saUnused.py script will check for the Service Account Insight. If an insist exists it will display the email and the project number:
{"service_account_email":
"example@developer.gserviceaccount.com", "project_number":
"123456789012"}
We do not recommend removing every service account without first investigating who owns it and what it was created for, but with this new information, you can begin to put a stop to credential sprawl in your GCP organization!
Conclusion
By using the Recommender service in GCP you are able to track down and identify unused service accounts across your entire GCP organization. By removing unused service accounts you are able to better track resources and minimize credential sprawl so that you can focus on only what’s actively being used in your cloud environment.
