Open Source Projects
Explore ScaleSec's Open Source Initiatives
-
All
-
HashiCorp
-
GCP
-
AWS
More about this Project
ScaleSec Vault AssistantSimplifying HashiCorp Vault installation and management.More about this Project
ScaleSec Secret StoreBuilding custom plugins made easy.
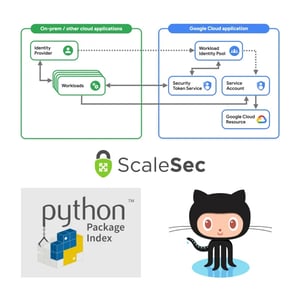
ScaleSec GCP Workload Identity FederationAccess GCP from AWS without static credentials.

ScaleSec GCP Unused Service Account ListerEasily identify idle Service Accounts.

ScaleSec Project LockdownAuto remediation for secure GCP environments.

ScaleSec GCP Organization Policy Bot100% Serverless policy updates to Slack & Twitter.

ScaleSec Vault AssistantInventory and export Keys effortlessly.

ScaleSec GCP Event Threat Detection RemediatorAutomate threat remediations.
ScaleSec Terraform AWS Service Control Policy SuitePolicies for AWS Organizations.